Vantaa, Finland June 2007
For more information:
Mr. Kimmo Rousku
How to crack Microsoft Windows Vista / XP-workstations and Windows 200x
servers in a minute?
Update - 21st June
Some free encryption programs:
There are
some freeware encryption software available:
- Free
open-source disk encryption software for Windows Vista/XP/2000 and Linux
http://www.ce-infosys.com/english/downloads/free_compusec/index.html
- so far no
Vista-version available
Before
you start using any encryption software, make sure you have fresh backups of
your computer. Read release notes and installation guides / requirements
carefully. I've managed once to encrypt my laptop so that I had to wait 8 days
before I was able to try my next password guess, I gave up after about 2 weeks
and lost couple of files...
================================================================
Update - 17th June
There are
many valuable links, which I'd like to recommend for further reading:
KB818200 -
An attacker with physical access to a computer may be able to access files and
other data http://support.microsoft.com/kb/818200/en-us
- published
31st May 2007 rev 10.
Reduce Your
Risk: 10 Security Rules To Live By http://www.microsoft.com/technet/technetmag/issues/2006/05/ReduceRisk/
May - June 2006 TechNet Magazine / Wes Miller
10
Immutable Laws of Security http://www.microsoft.com/technet/archive/community/columns/security/essays/10imlaws.mspx?mfr=true
================================================================
Update 12th June
Making IT easier...
Instead of pressing once "any key" and clicking four mouse clicks to
be able to start copying files to usb-disk, you can download Vista WAIK-tools
and make a WinPE-boot disk to make the cracking process easier. If you have
WinPE boot media, just press "any key" to boot it, wait a couple of
minutes and you have full access to your computer - no need for mouse clicks at
all.
There are few things I'd like to point out:
-
Yes, this is not a new method, I've been using
L0phtcrack etc since 90's
-
BUT this trick needs no special software nor technical
knowledge. Anyone can use this method at any computer, if physical access is
available. You don’t have to be able to speak C++ or to compile kernel.
-
Yes, as mentioned later in this page, BIOS-settings
can be removed /cracked, the computer's hard disk can be stolen and put to
another machine to be copied. Unfortunately there are some (older) bios-versions, which allows user
to choose between different boot devices even bios-passwords
enabled :-(
-
Summary: If you really want to secure your files and
systems, I highly recommend you to keep physical access to your computer as
tight as possible and ENCRYPT your hard disks.
================================================================
11th
June
My website http://www.ict-tuki.fi and this document
reveal and explain how anyone can crack almost any computer, which uses
Microsoft Windows operating system and which doesn’t include any special security
components (for example hard disk encryption).
This
security feature was found 8th February 2007 during Windows Vista
training session and reported immediately to Microsoft Finland Oyj. Further
investigations revealed that it is possible to crack other Windows OS versions,
too. Also this information was distributed to local Microsoft office. These
findings were confirmed 10th February 2007 by Microsoft Finland.
Four months
have passed and Microsoft hasn’t given any information nor warned its customers
concerning this dangerous feature. Therefore I have decided to inform about
this feature via my web pages. So, learn more about this phenomenon and please
secure your workstations and servers!
What’s the problem?
This problematic
security feature exists because Windows Vista Repair Computer / System Recovery
program enables the use of command prompt without any user authentication with
highest possible - system-level – priviledges.
Cracking
Windows operating systems has been possible by using cracking software found
from various web pages. This is the first time when cracking Windows operating
systems is really easy and needs no deeper technical knowledge. This is the
reason, why everyone using Windows should understand the cracking method and
start preparing safety systems, if needed.
1. Requirements:
a) Physical
access to workstation / server
b) Windows
Vista Installation-DVD-media
- It’s easy
to create a bootable USB flash memory that works in a similar way
- Windows
Home Basic, Premium, Business and Ultimate tested
c) For
example USB-memory to transfer files
Special
note: no user names or passwords are needed
2. Phase 1 – Booting
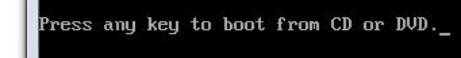
Start
Windows Vista installation from the installation-DVD (you may have to ”press
any key” in order to boot from DVD, this depends on the BIOS)
-
The
only realistic solution to keep OS secure, is to make it impossible to boot
from any other media than local hard disk.
-
Remember
to set up BIOS-password. After that it’s not easy to change the booting order.
-
As all
security experts know, resetting BIOS is possible if there’s free physical
access to the computer. If a cracker can open the cover of the computer, he can
use the motherboard’s BIOS reset functions to clear all existing passwords.
-
Another
highly recommended solution to protect the computer is hard disk encryption,
which unfortunately isn’t available for most Windows Vista users (only in
Enterprise or Ultimate versions). For Windows XP and older systems encrypting
is possible only by using 3rd party commercial software.
-
Encrypting
File System (EFS) could be a solution, too, but it’s not included in Windows
Home versions. Many corporate administrators have dropped EFS because of other
problems related to folder / file level encryption.
-
You
can also use a startup password, which can be enabled from BIOS-settings. In
corporate environment, managing a large number of startup passwords in a secure
way is a very complicated task.
3. Phase 2 – Language / Time
& currency / Keyboard selections
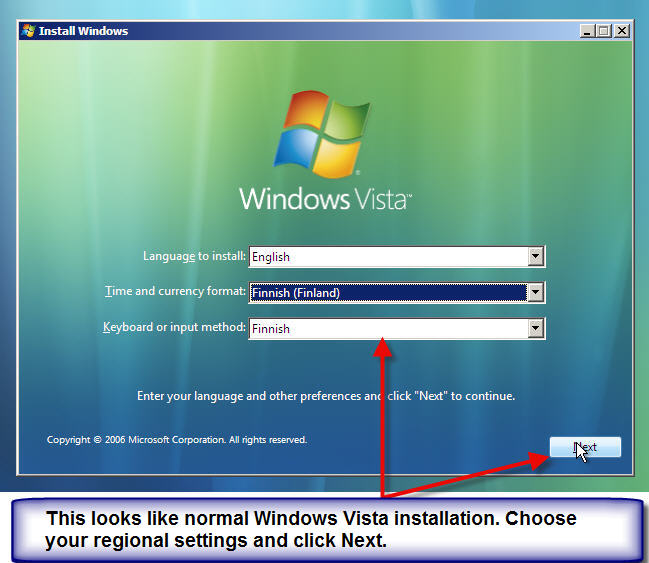
Select
Vista installation language and press Next
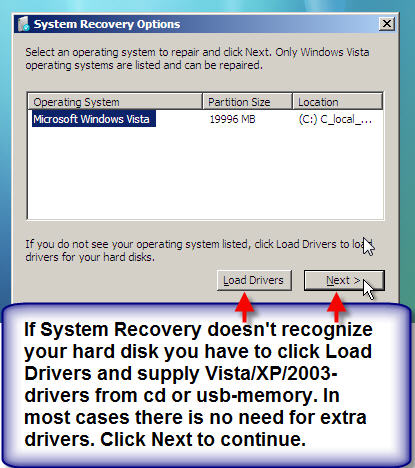
4. Phase 3 – Installation choices
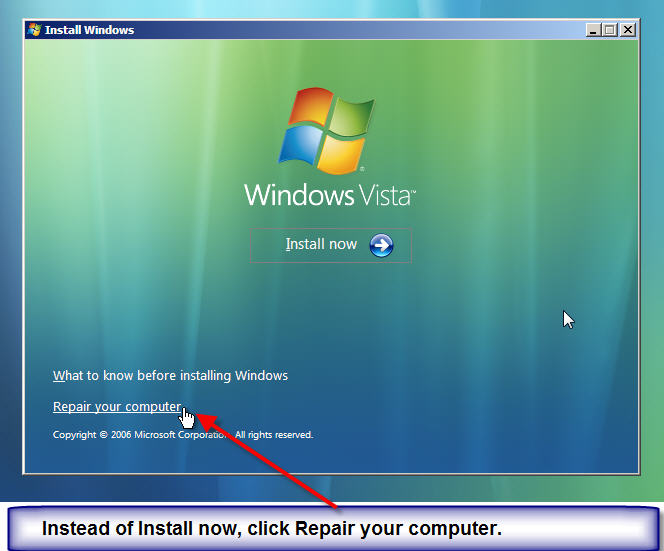
From the
main installation menu choose Repair your computer (do not choose Install now).
If
installation-DVD / System Recovery doesn’t recognize the local hard disk
because of a missing driver, a new driver can be loaded from the usb-disk or
cd. In most cases (even in my 2003 server crack test) it’s not needed, thanks
to Plug & Play, so choose Next
5. Phase 4 – Command prompt
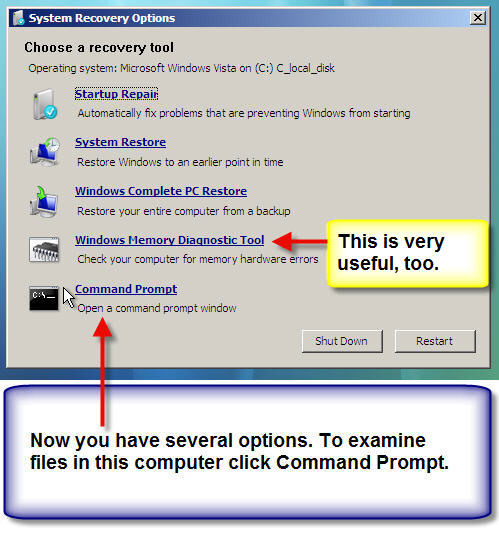
Choose Command
Prompt from the System Recovery Options menu.
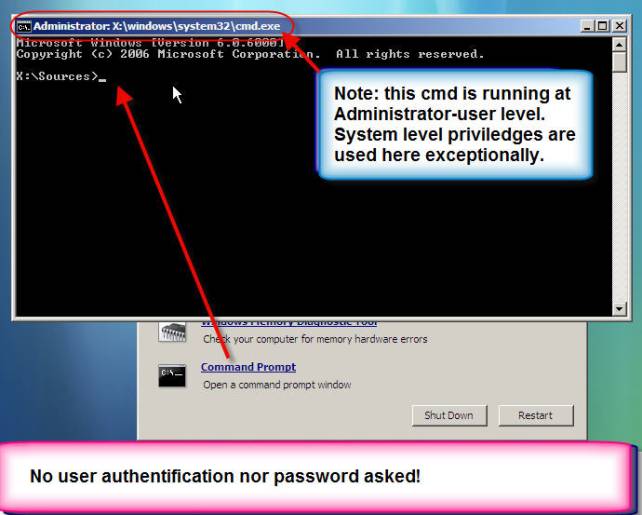
Voilà! Here
you have full access to this computer, not only as an administrator but also as
a system account user.
After this
you can insert usb-memory and copy any non-encrypted file from this computer to
usb-memory and steal information without leaving any marks to the system or
event viewer logs.
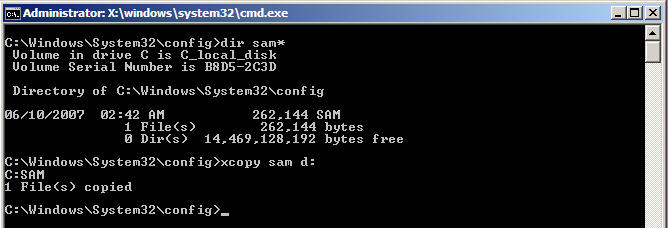
Also, you
could for example copy SAM-file (contains names and passwords of local users)
from c:\windows\system32\config to usb-memory and start cracking computer’s
user password at remote computer.
A cracker can:
1. … copy
files from hard disk to USB, floppy or network server
2. … create
/ modify / delete files and folders
3. … use
most of the MS-DOS like commands
4. … use
this method in Vista, XP, 200x
6. What does this mean?
Most
computers which use Microsoft Windows OS are vulnerable to local penetration,
if a cracker has full access to computer’s hard disk and knows how to use Vista
Installation-DVD System Recovery functions.
As a security expert, I believe this is a major security risk found in
Microsoft OS.
Even before
Vista, different methods were available for attacking Windows OS security,
t.ex. using programs which could be downloaded from the internet. However,
these methods have been either difficult to use or too demanding for normal
users.
Vista
Installation-DVD enables anyone to crack Windows OS easily
in minutes.
7. How is this possible?
It’s
possible, that the recovery command prompt has been intentionally included in
Windows Vista with system level user rights and without any authentication, for
example to ease problem solving etc. But ….
… by
default, there should always be some kind of user authentication, so that only
authenticated local administrators are entitled to use command prompt.
There is no
reasonable explanation why it’s possible to run this command prompt not only in
Vista but also in older Windows OS versions .
-
Quality
assurance error?
-
Not
enough testing?
8. Could Microsoft patch this
problem?
Is it possible
to modify the Repair Computer function in order to make it use authentification
(in every OS-versions)?
Is it
possible to block the use of Repair Computer function in other Windows OS’es?
There are
no instant solutions available, because millions of customers have already
purchased Vista.
However,
Microsoft could/ should inform about this security risk and give instructions
how to protect oneself against it:
•
How to
setup startup and BIOS passwords and change boot order
•
Recommendations
for disk encryption
I wish
there was an easy to use BitLocker-type disk encryption software free of charge
for all existing Windows OS’es including 2000-XP-Vista. Perhaps it’s now
understandable, that every version of Windows Server 2008 includes BitLocker
Hard Disk Encryption-technology.
9. Proof-of-concept
The
following picture demonstrates how to use this feature to crack and examine
files in a computer running Windows Vista. You can follow these instructions to
other computers running other versions of Windows operating systems.
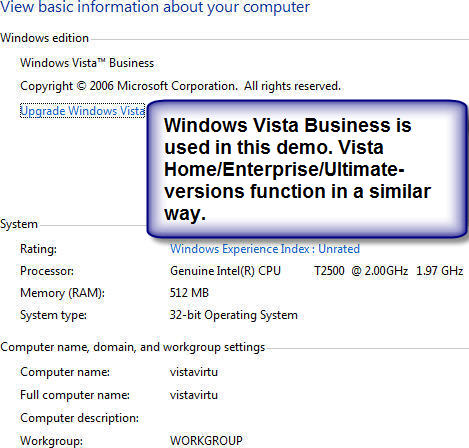
This P-O-C is done using Windows Vista Business
but you can expect similar results with other Windows operating systems.
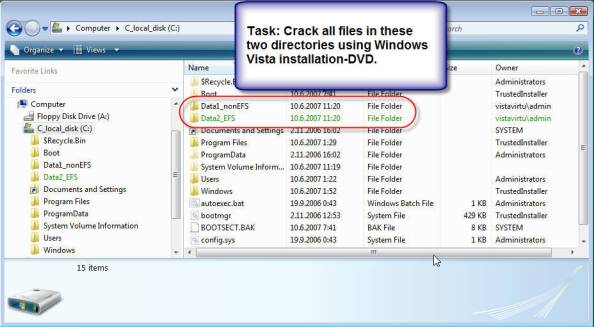
My computer
includes two folders in the root of c:-drive which I’d like to open using Vista
Recovery Options. These folders are Data1_nonEFS and Data2_EFS. First folder is
not encrypted, the other one is encrypted with EFS.
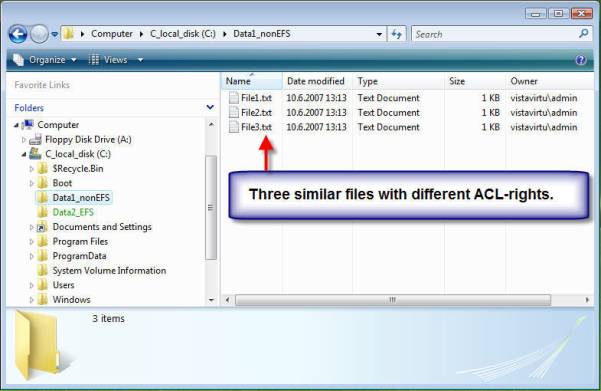
Both
folders have three files named File1.txt, File2.txt and File3.txt. Their
content is similar, but they have different access control list-rights.
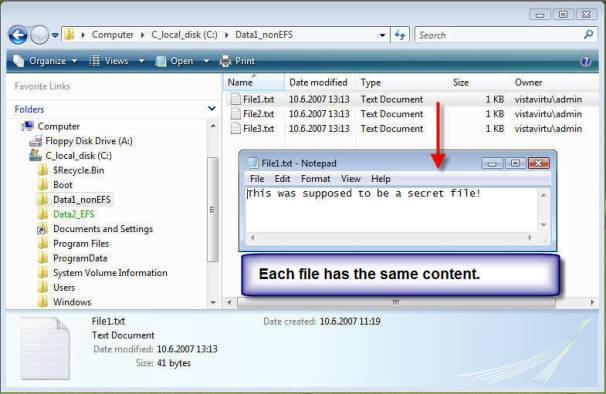
“This was
supposed to be a secret file!” is in each file.
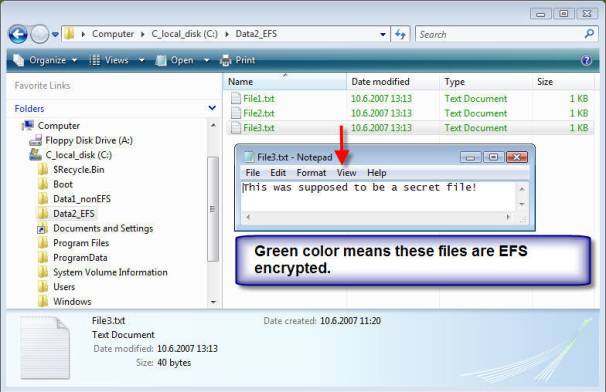
Files in
Data2_EFS-folder are encrypted using build in Encrypting Files System (EFS).
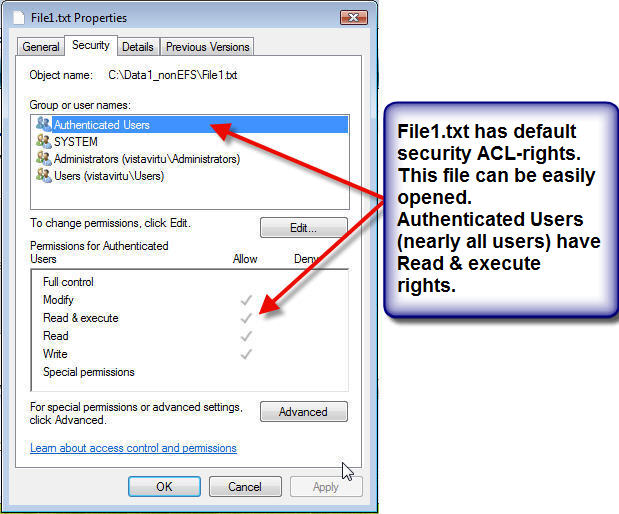
File1 has
default security ACL-rights, which consist of four users or groups with slightly
different permissions. Practically everyone who uses this computer can have
access to this file, because Authenticated Users group have Read &
Execute-rights.
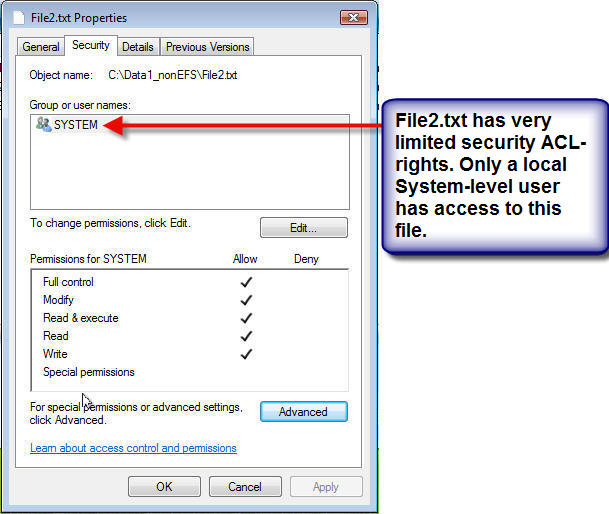
File2.txt
doesn’t include any typical user rights, instead there are rights only for System
to access this file. This is not a common permission, but it demonstrates, how
you can access even files like this in command prompt without any problems.
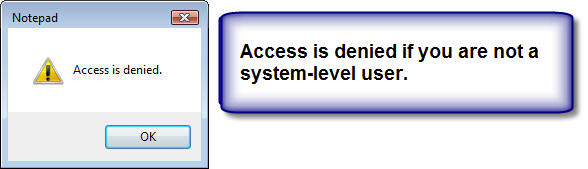
As you can
see, even local administrator users don’t have access to this file while
running Vista.
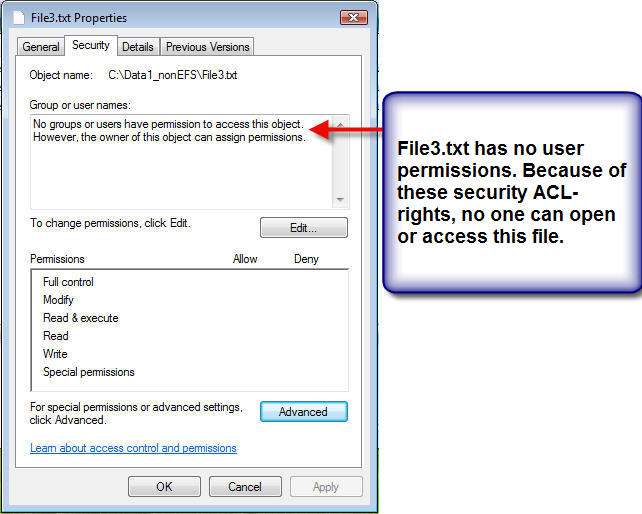
File3.txt –
there’s no permission to this file at all. As you will later notice, this is
not a problem while operating in command prompt if you know how to use two new
Windows Vista command line commands.
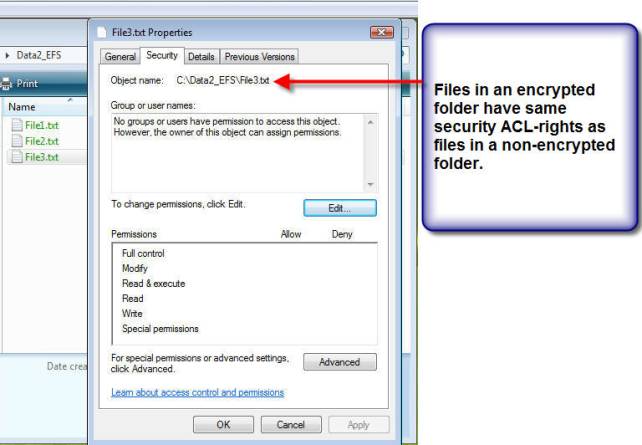
Data2_EFS-folder
contains three similarly named files. Their ACL-rights are the same as in
Data1_nonEFS-folder.
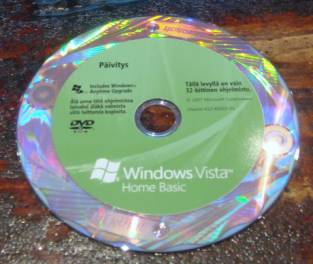
Start your
computer and insert Vista installation disk immediately to the dvd-drive.
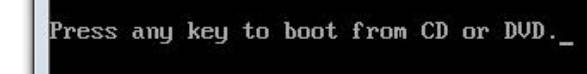
In case of
this notice, press quickly “any key”.
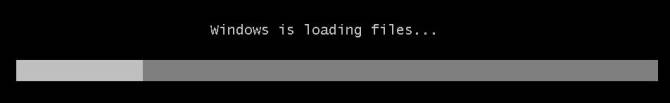
If you see
this text and bar, you’ve been quick enough. Otherwise, let Vista or other
operating system start normally, reboot system and try to be a little quicker
next time.
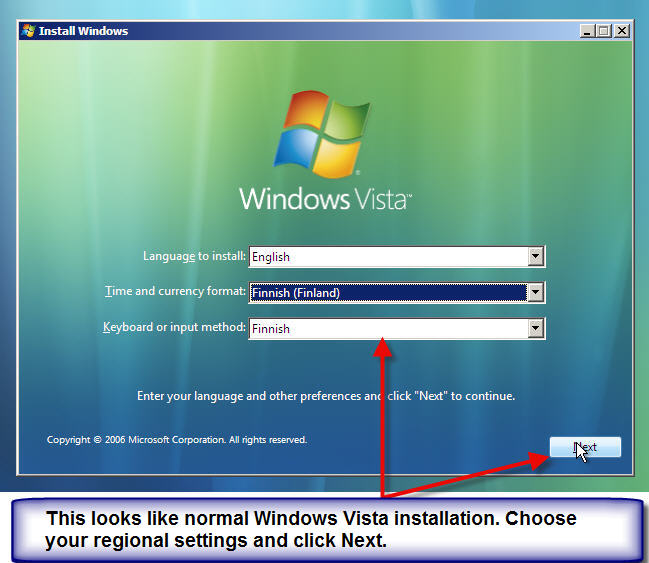
In this
case I choose Finnish time¤cy format and Finnish keyboard. Choose
your own settings and click Next.
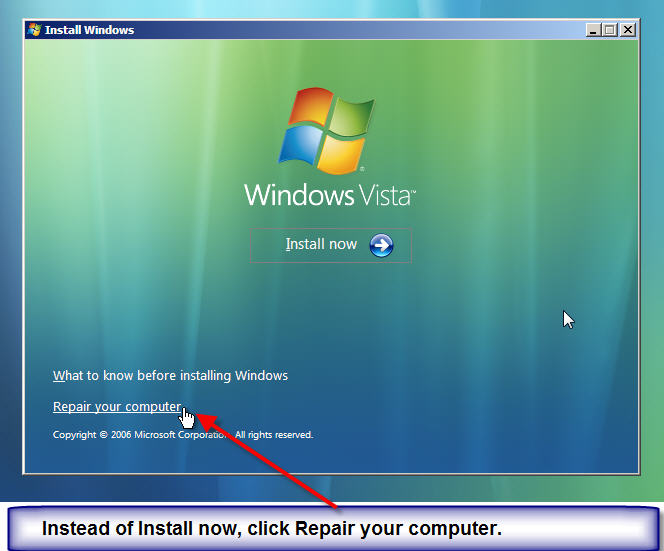
Normally
you’d click Install now. This time, click Repair your computer to enter System
Recovery options.
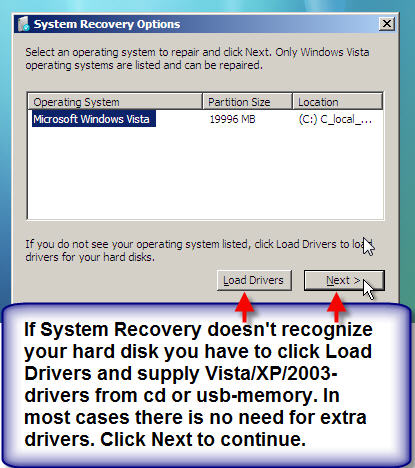
In some
systems, Vista installation media doesn’t include necessary hard disk drivers.
In such case, click Load Drivers and supply drivers needed to get access to
hard disk. You can try to use older Windows version drivers, if Vista drivers
are not available. If you see the operating system you’d like to enter, click
Next to continue.
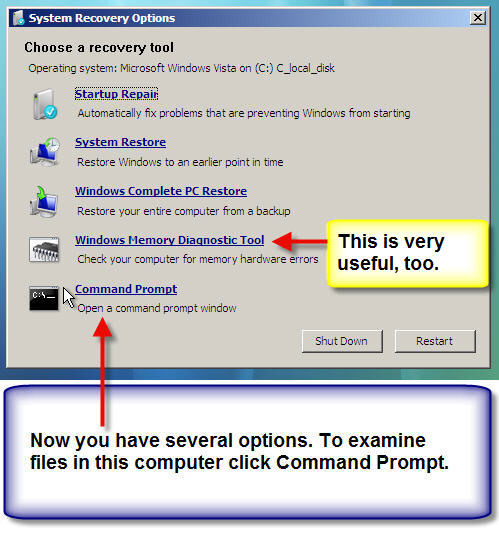
Unless
there are no problems with hard disk drivers, you’ll enter the System Recovery
Options menu. There are five options you can choose from, but in this case
Command Prompt is what we are looking for.
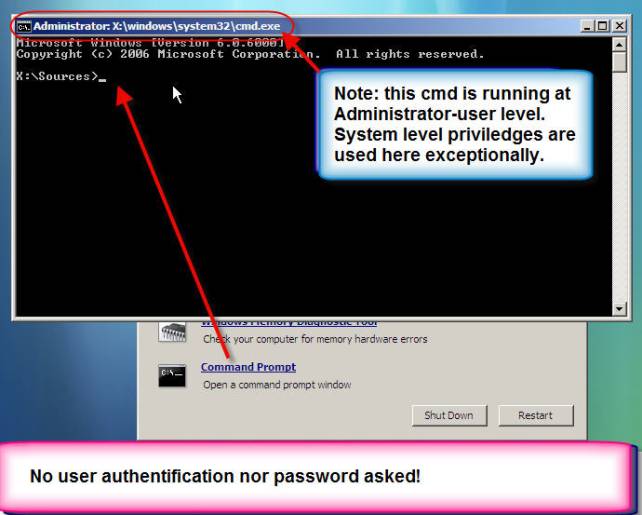
As you can
see, you’ll enter a typical cmd-prompt. X:\Sources is your default folder.
Actually, you have entered WindowsPE recovery mode. Here you have many
ms-dos-like commands available; use Help to see a list of commands available.
The most stunning thing is that there is no kind of a user authentification
when entering this command prompt! For security reasons, even basic local
administrator authentification would be enough as used in older Windows
versions’ recovery consoles.
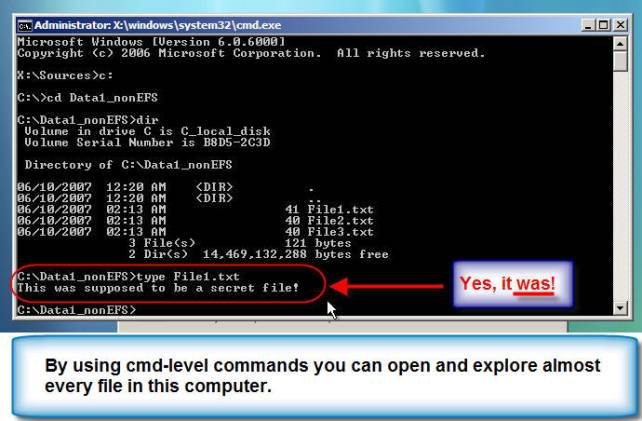
By using
only four commands, you can find out what File1.txt-file contains! As you can
remember, this file was intentionally left unchanged so that any authenticated
user could have access to it.
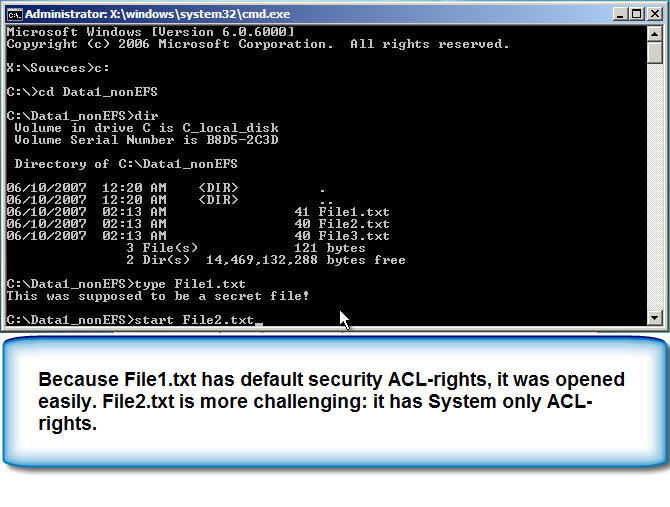 Next
mission is to open File2.txt. Instead of type-command, I’ll to open it into
notepad using start File2.txt command.
Next
mission is to open File2.txt. Instead of type-command, I’ll to open it into
notepad using start File2.txt command.
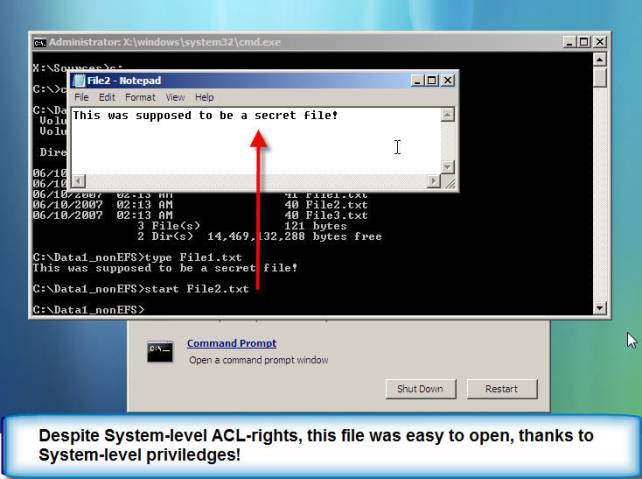
Notepad
opens and shows File2.txt contents! And the only acl-right in this file was
given to System:
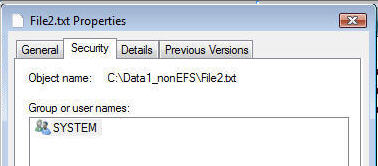
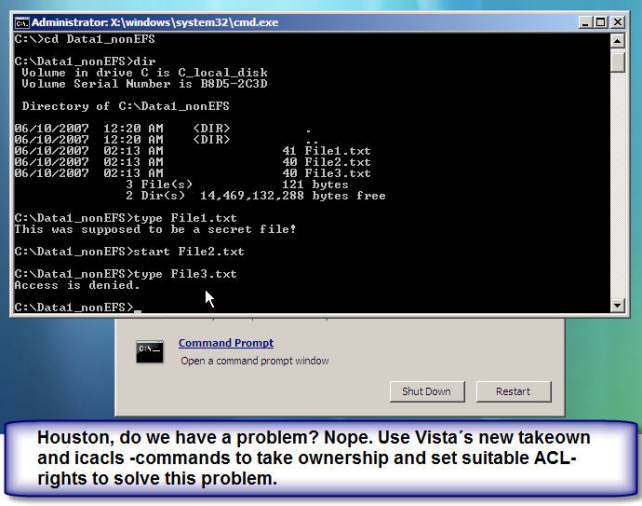
What about
File3.txt, which has no permissions at all? Fortunately, Windows Vista has a a
league of new command line utilities, which are in this case very handy.
Takeown-command
makes it possible to take ownership in command line. After you have become the
owner of File3.txt, you can set ACL-rights by using a new icacls-command, which
replaces the old cacls-command. Now you have full access to File3.txt.
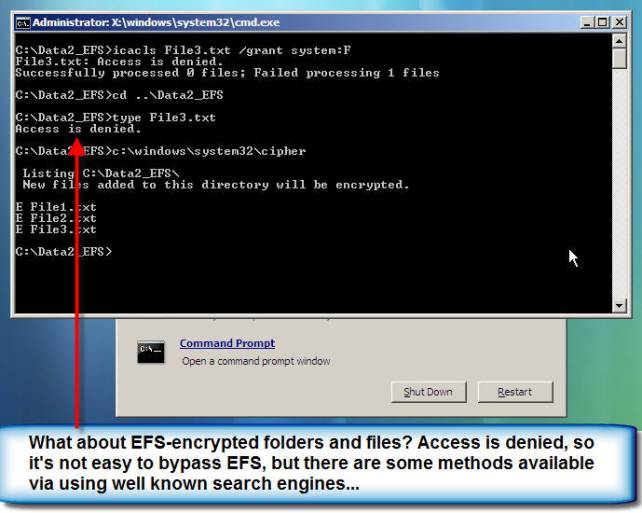
After
opening all three files in C:\Data2_nonEFS-folders, let’s have a look at
C:\Data2_EFS-folder. Because this folder is encrypted using EFS, there is no
simple method in my knowledge to open these encrypted files in the command
prompt.
Summary:
To protect
you computer or workstation, try to:
-
setup
bios boot order so that booting from other media than hard disk is not possible
-
setup
startup password from your bios (mainly in home computers)
-
use
hard disk encryption software, if possible
-
encrypt
files and folders using EFS, if mechanisms above are not possible
